The office perimeter is gone. Your security model needs to reflect that reality.
The pandemic did not invent remote working, but it made it permanent. What began as a temporary emergency measure in early 2020 has become the default operating model for millions of businesses. According to the ONS, more than 40% of UK workers now spend at least part of their week working from home. For knowledge workers in sectors like technology, professional services, and finance, the figure is closer to 70%.
This shift has been overwhelmingly positive for productivity, recruitment, and employee wellbeing. But it has also fundamentally dismantled the security model that most organisations relied on for decades. The traditional approach was simple: put a firewall at the edge of your network, control what comes in and what goes out, and trust everything inside the perimeter. When everyone worked in the same building, connected to the same network, using devices that never left the premises, this was a reasonable strategy.
That world no longer exists. Your employees now work from kitchen tables, spare bedrooms, co-working spaces, trains, and coffee shops. They connect through home broadband, mobile hotspots, and hotel WiFi. Their devices leave your building every evening and return every morning, if they return at all. The network perimeter has not just expanded; it has dissolved entirely. And if your security strategy still assumes that the office is the boundary, you are protecting a building while your data travels the country.

Home network security
The home network is the weakest link in most remote working setups. Unlike corporate networks, which are managed by IT professionals with commercial-grade equipment, home networks are consumer-grade, shared with family members, and rarely configured with security in mind.
Under the updated Cyber Essentials scheme, home routers are now explicitly in scope when staff connect work devices through them. You do not need to manage the router itself, but you do need to ensure that devices are protected regardless of what network they sit on. The practical implication is clear: you cannot trust the network, so you must secure the device.
Change the default router credentials
Every consumer router ships with a default admin username and password, typically printed on a sticker on the back of the device. These defaults are well known to attackers and widely published online. If your employee’s home router is still using admin/admin or the factory-set passphrase, anyone on the local network, or anyone who has exploited a known vulnerability in that router model, can reconfigure the device at will. That means redirecting DNS, injecting malicious content, or quietly monitoring all traffic. Changing the admin password is a two-minute job. Failing to do it is an open invitation.
Enforce WPA3 or WPA2 encryption
WiFi encryption determines whether traffic between a device and the router can be intercepted. WPA3 is the current standard and should be used wherever supported. WPA2 with AES remains acceptable. Anything older, including WPA with TKIP and the long-obsolete WEP protocol, is trivially breakable with tools freely available on the internet. The challenge for IT teams is that they do not control home routers. The practical response is to issue clear guidance to staff, include router configuration in onboarding checklists, and ensure device-level protections (encrypted connections, always-on VPN or ZTNA) compensate for networks you cannot verify.
Use a strong WiFi passphrase
A weak WiFi password is the easiest way for a neighbour, a visitor, or a determined attacker parked outside to gain access to the home network. Once on the network, they can see other devices, attempt lateral movement, and intercept unencrypted traffic. The guidance is simple: at least 16 characters, not a dictionary word, and not shared with anyone who does not need it. Encourage staff to treat their WiFi password like any other credential. If their teenage children have given it to every friend in the neighbourhood, it is time to change it.
Keep router firmware updated
Home router vulnerabilities are discovered regularly. In 2024 alone, critical flaws were found in widely deployed models from TP-Link, Netgear, and ASUS. Most consumer routers do not update automatically, and most home users never check for firmware updates manually. This creates a persistent, invisible attack surface. The best practice is to enable automatic updates where the router supports it, or to set a quarterly reminder to check the manufacturer’s website. For organisations with higher risk profiles, issuing managed routers or mobile hotspot devices to remote staff eliminates the variable entirely.
“The perimeter used to be a firewall at the edge of your network. Now the perimeter is every device, every identity, and every connection your employees make, from wherever they happen to be working today.”
VPN vs Zero Trust: choosing the right access model
How your remote workers connect to company resources is one of the most consequential security decisions you will make. The two dominant approaches represent fundamentally different philosophies about trust, access, and risk.
The tunnel approach
A traditional VPN creates an encrypted tunnel between the remote device and the corporate network. Once connected, the user’s device appears to be inside the network perimeter, with access to everything that implies: file shares, printers, internal applications, and other devices on the LAN. This model was designed for a world where the network was the trust boundary. It worked well when remote access was the exception rather than the rule, when a handful of road warriors needed to connect to the office server after hours. It was never designed for a scenario where the majority of the workforce connects remotely, every day, from dozens of different locations.
The fundamental weakness is excessive trust. Once a VPN connection is established, the user typically has broad network access. If that device is compromised, the attacker inherits the same access. VPN concentrators also create a single point of failure and a high-value target for attackers.
The identity-first approach
Zero Trust Network Access, commonly abbreviated to ZTNA, takes a fundamentally different approach. Instead of placing the user on the network and trusting them because they authenticated, ZTNA verifies every request individually. Access is granted to specific applications, not to the network itself. The user never sees the broader network. They connect to the application they need, and nothing else. If one application is compromised, lateral movement is contained because there is no network-level access to move across.
ZTNA aligns with how modern businesses actually operate. When your applications are in Microsoft 365, your CRM is SaaS, and your file storage is in SharePoint or OneDrive, putting users on a network to reach cloud services makes no sense. You are routing traffic backwards through your infrastructure for no security benefit.

Device security for remote workers
When you cannot trust the network, the device becomes the security boundary. Every control that matters, encryption, endpoint protection, firewall, patch compliance, must be enforced at the device level. This is not a new concept, but the shift to widespread remote working has made it the primary security strategy rather than a supplementary one.
Company-managed devices as the baseline
The single most effective control for remote worker security is ensuring that work happens on company-owned, company-managed devices. When you control the device, you control the security posture. You can enforce encryption, deploy endpoint protection, push configuration baselines through Intune or a similar MDM platform, and remotely wipe the device if it is lost or stolen. You know what software is installed, you know when patches are applied, and you can prove all of this to an auditor. Personal devices offer none of these guarantees. The cost of issuing a laptop to every employee is modest compared to the cost of a data breach caused by an unmanaged device.
Endpoint protection on every device
Every device that accesses organisational data needs active endpoint protection. This means a managed EDR or antivirus solution, not just the default Windows Defender in its out-of-the-box configuration. The key requirements are central management, automatic updates, real-time scanning, and reporting that your IT team can actually monitor. If a device is compromised while working from a home network or a hotel lobby, you need to know about it immediately, not when the user happens to mention something odd three weeks later.
Full disk encryption as standard
If a laptop is stolen from a home office, a car, or a coffee shop, full disk encryption is the difference between a lost device and a data breach. BitLocker on Windows and FileVault on macOS are built into the operating system and cost nothing to enable. Managed through Intune, you can enforce encryption across your fleet and escrow recovery keys centrally. There is no justification for any work device, whether company-owned or BYOD, accessing organisational data without full disk encryption enabled.
Software firewall enabled and configured
Home networks are shared environments. The same WiFi that carries your finance director’s Teams calls also serves smart TVs, gaming consoles, and children’s tablets. A software firewall on the work device is the boundary you can control when the network boundary belongs to someone else. The built-in OS firewall, properly configured, prevents unsolicited inbound connections and limits the attack surface when the device is on an untrusted network. This is a basic control, but it is also one of the most commonly overlooked.
Automatic updates and patch compliance
Remote devices are harder to patch than office-based machines. They are not always connected to the corporate network, they may be on slow home broadband connections, and users are more likely to defer updates when they are in the middle of work. Despite this, the requirement is the same: critical patches within 14 days, unsupported software removed or replaced. Intune, Autopatch, and similar tools make this manageable at scale, but it requires active monitoring. A device that has not checked in for 30 days is a device you cannot trust.
BYOD: the pragmatic compromise
In an ideal world, every employee would work on a company-managed device. In the real world, BYOD (Bring Your Own Device) is a fact of life for many organisations, whether by policy or by necessity. Startups cannot always afford hardware for every new hire. Contractors arrive with their own equipment. Executives insist on using their preferred devices.
The question is not whether to allow BYOD. It is how to allow it without creating unacceptable risk. The answer lies in separating the management of company data from the management of the device itself.
Application-level management with MAM
When personal devices must be used, Microsoft Intune’s Mobile Application Management (MAM) allows you to protect company data at the application level without managing the entire device. This means you can enforce encryption on Outlook data, prevent copy-paste from Teams to personal apps, and remotely wipe company data if the employee leaves, all without touching personal photos, messages, or applications. It is a pragmatic compromise that respects employee privacy while maintaining a meaningful security boundary.
Conditional access policies
Conditional access is the enforcement layer that makes BYOD viable for security-conscious organisations. You define rules: the device must be compliant, MFA must be completed, the sign-in must come from a recognised location or pass a risk assessment. If any condition is not met, access is blocked or additional verification is required. This means a personal device can access company email, but only if it meets your minimum security requirements. The device does not need to be fully managed; it just needs to prove that it is trustworthy enough for the resource being accessed.
Clear acceptable use policies
Technology alone cannot solve the BYOD challenge. You need clear, written policies that set expectations: what data can be accessed from personal devices, what applications are permitted, what happens to company data when someone leaves, and what rights the organisation has to wipe or inspect data on personal devices. Ambiguity creates risk. If employees do not understand the boundaries, they will make their own decisions, and those decisions will not always be the ones your security team would choose.
The hidden cost of BYOD
BYOD appears cheaper than issuing company devices. In practice, the cost often shifts from capital expenditure on hardware to operational expenditure on support, policy management, and incident response. Personal devices run different operating systems, different versions, different configurations. They break in ways your IT team cannot predict, and troubleshooting takes longer because you do not control the environment. For many SMEs, the total cost of ownership for a managed company device is lower than the total cost of supporting BYOD securely.
“You don’t need to manage the home router. You need to make the home router irrelevant. Secure the device, secure the identity, encrypt the connection. The network becomes a transport layer, not a trust boundary.”
Public WiFi: the risks are not theoretical
Coffee shops, hotels, airports, trains. Public WiFi is everywhere, and it is convenient. It is also inherently insecure. Open networks broadcast traffic in the clear. Even password-protected public networks share that password with every guest. When your employees connect to these networks, they are sharing a connection with unknown, unvetted, and potentially hostile users.
Man-in-the-middle attacks
On an open or poorly secured WiFi network, an attacker can position themselves between the user and the access point, intercepting and potentially modifying all traffic. While HTTPS protects the content of web traffic, DNS queries, metadata, and connections to services using older protocols may still be exposed. Captive portals, the login pages you see at hotels and airports, are a particularly common vector for credential harvesting.
Evil twin networks
An attacker creates a WiFi network with the same name as a legitimate one. Your device connects automatically because it remembers the SSID from a previous visit. All traffic now flows through the attacker’s equipment. This is trivially easy to execute with commodity hardware and freely available software. Your employees may be connected to a malicious network without any visible indication that anything is wrong.
Network sniffing and session hijacking
Even passive monitoring of a public network can yield valuable intelligence: which services your employees use, when they log in, what metadata leaks from their connections. Active attacks can go further, potentially hijacking authenticated sessions or injecting content into unencrypted connections. The risk is not theoretical; it is a documented and well-understood attack category that requires minimal skill to execute.
Practical mitigation
The safest policy is to avoid public WiFi entirely for work. Where that is not practical, always-on VPN or ZTNA ensures traffic is encrypted regardless of the underlying network. Mobile hotspots using 4G or 5G connectivity are a more secure alternative, and the cost of a data SIM is trivial compared to the risk. If public WiFi must be used, ensure all connections are encrypted, avoid logging into sensitive services, and treat the network as actively hostile.
The cloud-first approach for SMEs
The most effective way to secure a distributed workforce is to eliminate the need for remote access to on-premises resources in the first place. If your data is in the cloud, your applications are SaaS, and your identity platform is cloud-native, then the question of “how do remote workers connect to the office” becomes irrelevant. They do not need to. The office is wherever they are, and the security controls travel with them.
Identity is the new perimeter
When your applications are cloud-hosted and your users are distributed, the network perimeter is no longer the meaningful trust boundary. Identity is. Every access decision should start with: who is this user, what device are they on, where are they connecting from, and what are they trying to access? Multi-factor authentication, conditional access policies, and risk-based sign-in evaluation form the new perimeter. If your identity infrastructure is not robust, nothing else matters, because every other control depends on knowing who the user actually is.
Microsoft 365 as the security platform
For SMEs already using Microsoft 365, the security tooling is largely built in. Azure Active Directory (now Entra ID) provides identity and access management. Intune provides device management. Defender for Endpoint provides threat protection. Conditional access ties it all together. The challenge is not acquiring the tools; it is configuring them properly. Most SMEs are paying for security features they have never enabled. A well-configured Microsoft 365 Business Premium tenant provides enterprise-grade security at an SME price point.
Reduce the on-premises footprint
Every on-premises server, every local file share, every piece of network hardware is something that remote workers need to reach, and something that needs protecting from an expanded attack surface. Moving file storage to SharePoint, email to Exchange Online, and line-of-business applications to SaaS equivalents does not just improve accessibility for remote workers. It shifts security responsibility to providers with dedicated security teams, 24/7 monitoring, and infrastructure that most SMEs could never replicate. The fewer on-premises resources you maintain, the less your remote workers need to connect back to your network.
Monitor, detect, respond
Visibility is the foundation of security. If you cannot see what is happening across your environment, you cannot detect threats, investigate incidents, or prove compliance. For remote workforces, this means centralised logging, endpoint telemetry, sign-in monitoring, and alerting for anomalous behaviour. Tools like Microsoft Sentinel or a managed SIEM service aggregate signals from across your estate and surface threats that would be invisible if you were only watching one system at a time. Security without monitoring is guesswork.
Test your assumptions regularly
The security controls you configured six months ago may not reflect your current reality. New staff, new devices, new applications, changes in working patterns: all of these can introduce gaps. Regular reviews, at least quarterly, should verify that conditional access policies are enforced, devices are compliant, MFA adoption is complete, and your asset inventory is current. Penetration testing and simulated phishing exercises validate whether your controls work in practice, not just in policy documents.
Security that works with how people actually work
The biggest mistake organisations make with remote working security is treating it as a separate problem. It is not. Remote working is working. The security model should not distinguish between someone sitting in the office and someone sitting at home. If your controls only work when people are on the corporate network, they do not work at all.
The best remote working security is invisible to the user. Conditional access runs in the background. MFA is a quick tap on a phone. Endpoint protection operates silently. Encryption is automatic. Patches install overnight. The user opens their laptop, authenticates, and gets to work. They do not think about security, because the security is built into the platform, not bolted on as an afterthought.
Conversely, security that creates friction will be circumvented. If the VPN is slow, people will disconnect it. If MFA is cumbersome, people will find workarounds. If company devices are locked down to the point of being unusable, people will use their personal devices instead. Every security control that degrades the user experience creates a corresponding incentive to bypass it. The goal is security that is strong enough to be effective and smooth enough to be accepted.
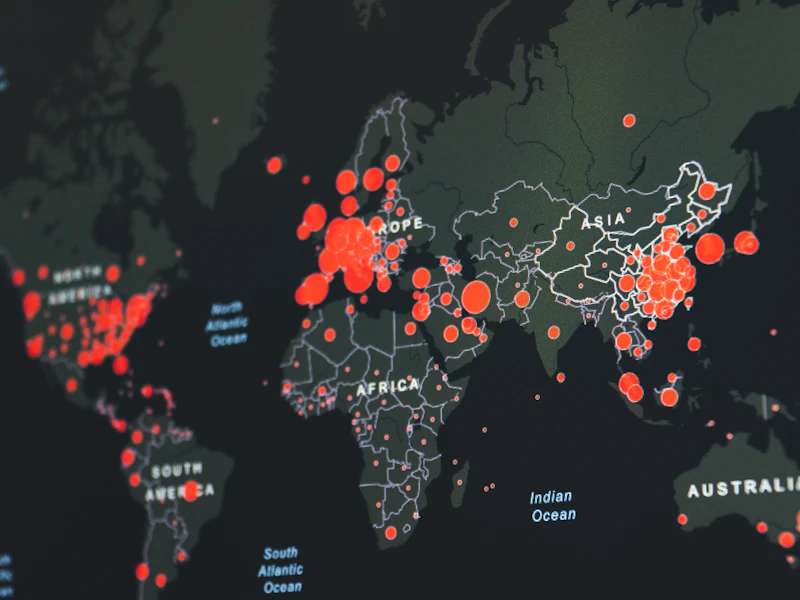
The numbers behind the shift
Remote working is not a temporary arrangement. The data tells a clear story: distributed work is the permanent reality, and security must adapt accordingly.
of UK workers now spend at least part of their week working remotely
of data breaches in 2025 involved remote worker endpoints as the initial vector
more likely to click a phishing link when working outside the office
Need help securing your remote workforce?
We help UK businesses design and implement remote working security that is robust, practical, and invisible to end users. That includes device management with Intune, conditional access configuration, ZTNA deployment, endpoint protection, and the policies that tie it all together.
If you are not sure whether your current setup is secure enough, a remote working security review takes around an hour and will give you a clear picture of where you stand and what needs to change.



