Practical guides. Honest advice. No fluff.
Practical guides, checklists, and tools to help you improve your IT and security. Written by the people who do the work, not a marketing team.
Articles

Email Fraud & Invoice Manipulation
How UK businesses lose money to business email compromise
Firefighting vs Managed IT
The true cost of reactive vs proactive IT support
M365 Backup vs Retention
Why retention policies aren't the same as backup

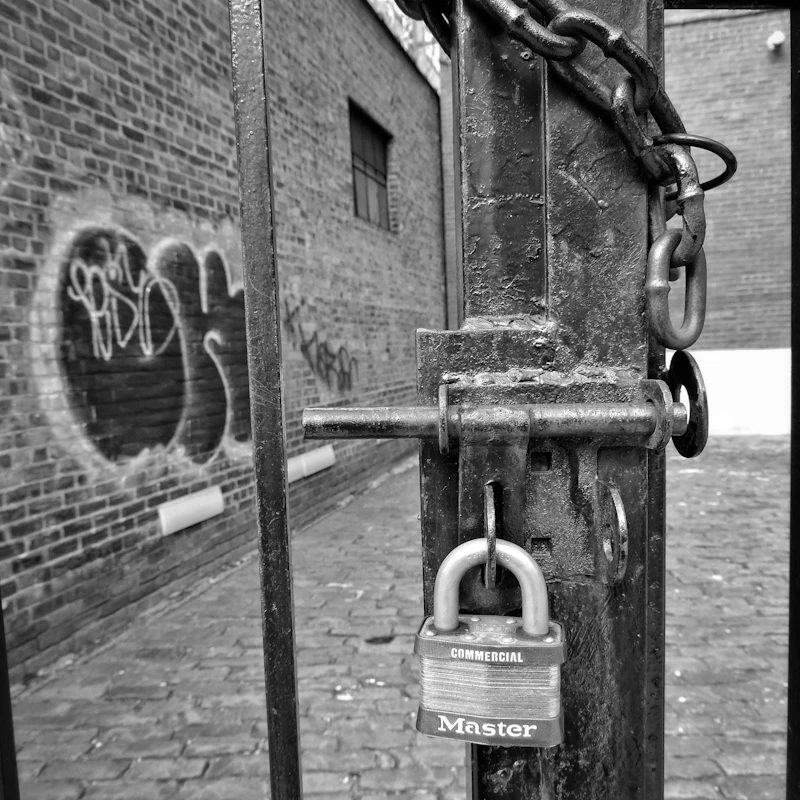
Why 'Break-Fix' IT No Longer Works
The hidden costs of reactive IT support
Understanding Cyber Insurance
What insurers actually look for in SME cyber security
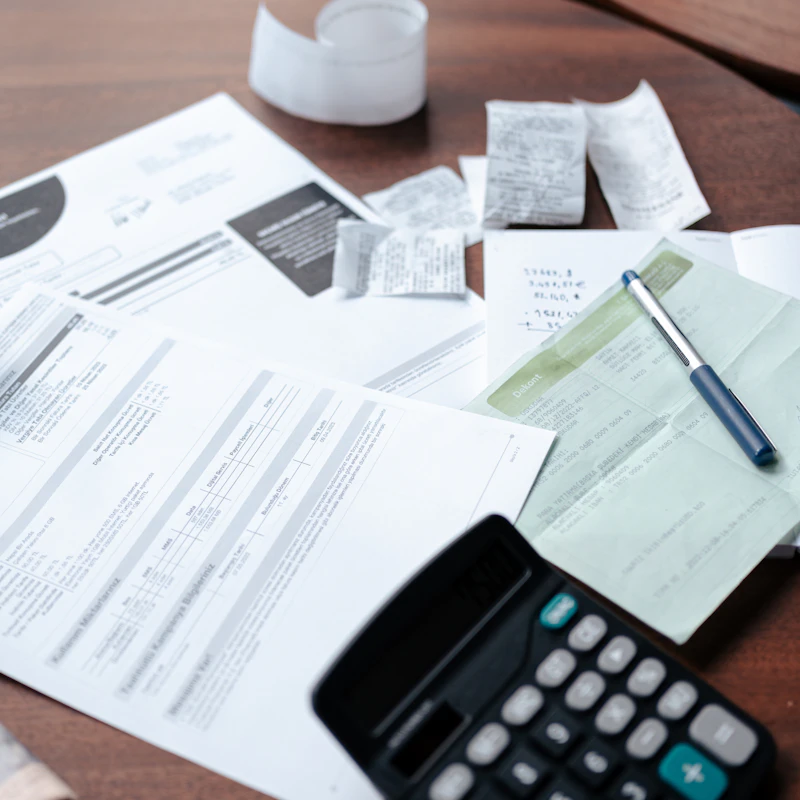
The Real Cost of Poor IT
How to calculate the business impact of IT problems
Checklists
Small Business Cyber Checklist
The 60-minute security review any business can complete today
Choosing an MSP
A buyer's checklist and the red flags to watch for
Device Security Standard
What every work laptop should have configured

Leaver Offboarding Checklist
Complete IT offboarding process for departing staff
SaaS Sprawl Audit
Cutting waste and reducing risk from uncontrolled subscriptions

Cyber Essentials Readiness
Prepare for Cyber Essentials certification
Backup & Recovery Checklist
Ensure your backups are configured correctly and tested regularly
Guides
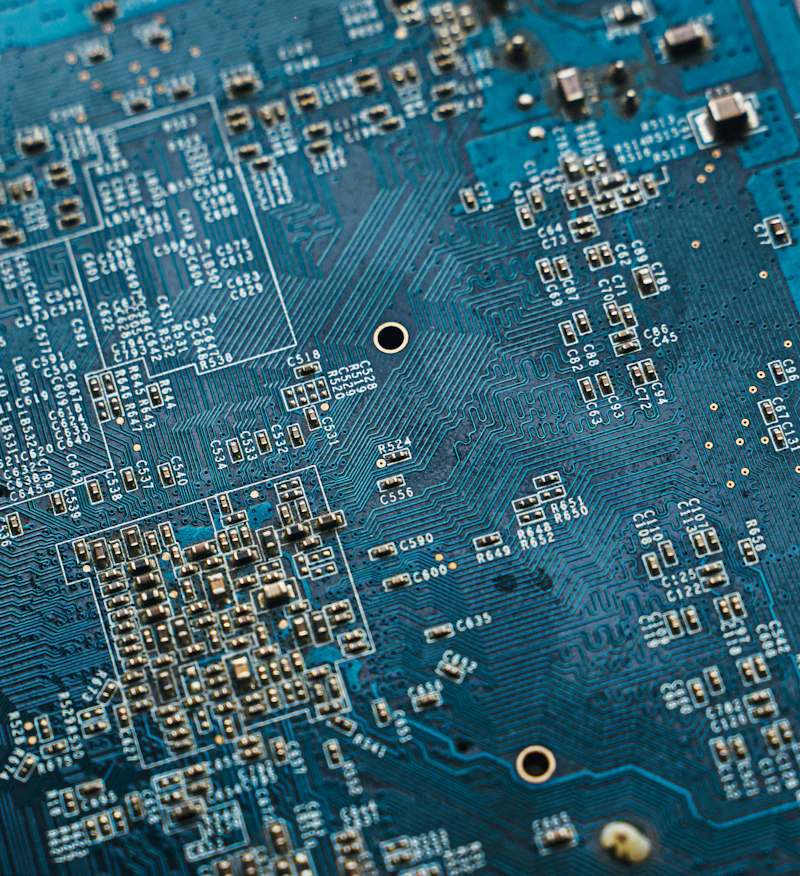
Cyber Essentials in 2026
What it is, what's changing, and how to prepare
Microsoft 365 Security Settings
The 10 settings most tenants miss
Ransomware-Resistant Backups
What 'good' looks like in 2026

Incident Response for SMEs
What to do in the first 24 hours
Microsoft 365 Copilot Readiness
Governance, permissions, and safe rollout

Business Continuity for SMEs
Staying operational through outages
Cyber Action Plan
Using the Cyber Action Toolkit effectively
M365 Business Premium Explained
What's included and whether you need it

MFA Best Practices
What to enforce and common mistakes
Conditional Access Basics
Implementing conditional access for SMEs

Passwordless Security
Passkeys, Authenticator, and Windows Hello
Admin Access Control
Reducing risk without blocking work
Patch Management
Keeping systems updated without pain
Endpoint Protection Guide
What 'good' looks like for device security
Secure Remote Working
Home WiFi, VPN vs ZTNA, and best practices

Teams Governance
Guests, naming conventions, and sprawl control
SharePoint Permissions Made Simple
Understanding and managing SharePoint access

Vendor & Supply Chain Risk
Managing security risks from suppliers
Cyber Insurance Readiness
What insurers look for and how to get better coverage
IT Health Check Explained
What we assess and why it matters
SME Technology Planning
Align technology investments with business goals

M365 Security Baseline
Essential security settings for M365 environments
Technical Project Management
Why IT projects fail without it and what good looks like
Templates

New Starter IT Setup
A 7-day onboarding plan for new employees
Incident Communications Pack
Templates for staff and customer communications
Incident Response Template
Ready-to-use template for documenting incidents
IT Budget Planning Worksheet
Plan your technology spending and refresh cycles



